Background and Timeline: A 70-year-old businessman residing in Mumbai’s upscale Malabar Hill area fell victim to a deceptive FASTag activation trap in January 2026. The ordeal began when the victim searched Google for an authorized agent after his vehicle’s FASTag stopped functioning correctly. Believing he was contacting a legitimate support representative, he engaged with a phone number obtained through the search results, which led to a devastating financial loss.
Modus Operandi: The fraudster impersonated a customer service agent and assured the victim that his FASTag would be activated immediately via an online procedure. He sent a malicious link that directed the businessman to a phishing webpage designed to harvest sensitive personal and bank account details. While the victim sensed something was wrong and closed the page, the scammers had already captured his information, waiting two days before siphoning the funds to avoid immediate detection.
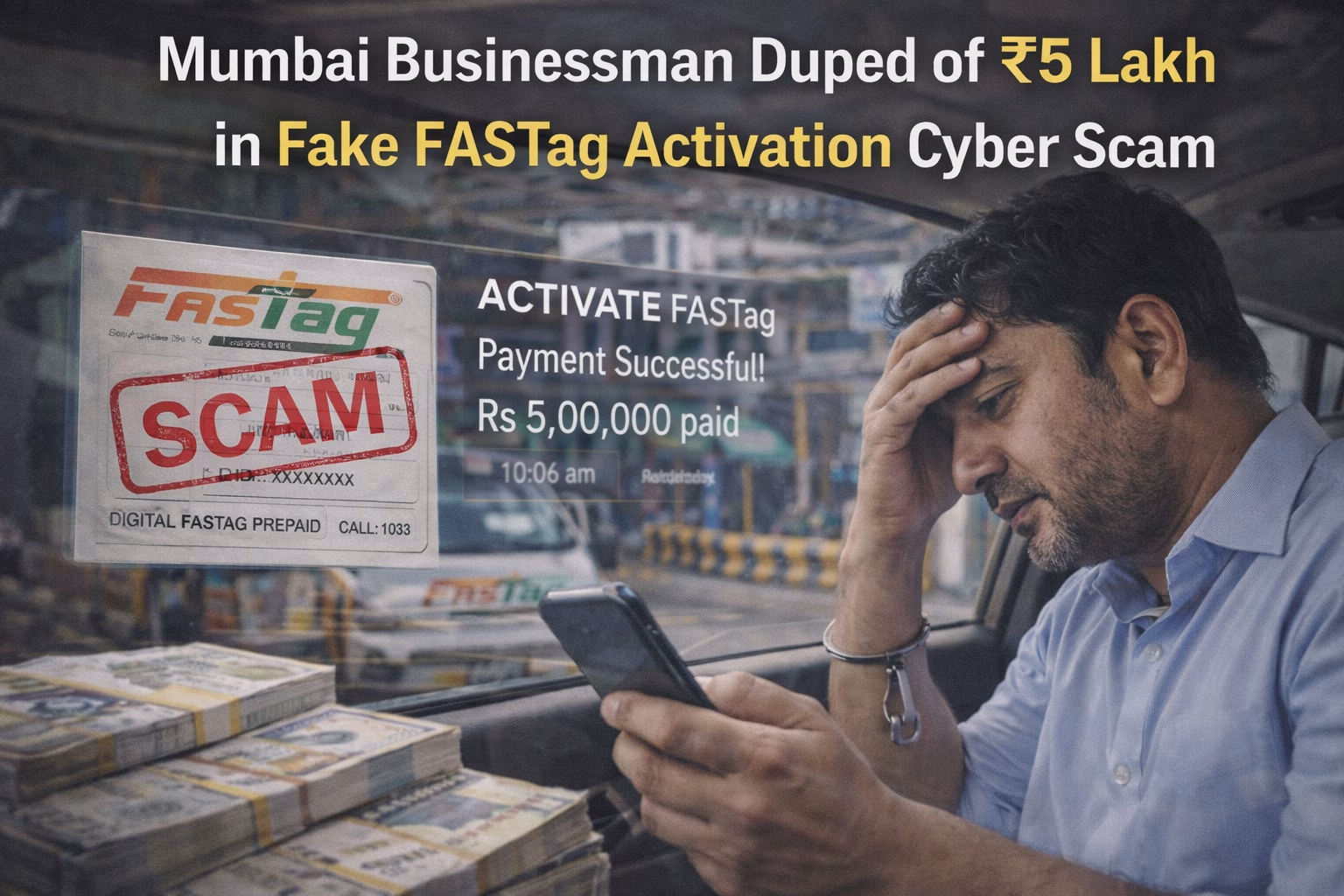
Victims and Financial Impact: The elderly businessman suffered a total financial loss of ₹5 lakh, which was siphoned from two separate accounts. Specifically, ₹4 lakh was transferred from his personal account, while an additional ₹1 lakh was stolen from his wife’s bank account. This case highlights how scammers can use a single point of data entry to compromise multiple family members through linked financial profiles.
Investigation and Agencies Involved: The Mumbai Cyber Police and the local station at Malabar Hill are investigating the digital footprints left by the phishing website. Authorities are tracing the destination accounts where the ₹5 lakh was deposited, which are suspected to be mule accounts managed by an interstate syndicate. The investigation is also focusing on the “SEO poisoning” tactics used to place the fraudulent number at the top of Google search results.
Arrests and Suspects: No immediate arrests have been reported as of the digest date, though several leads regarding the domain registration of the phishing link are being pursued. Police are looking for the individuals who managed the phone number used to contact the victim and the beneficiaries of the unauthorized transfers. Investigators have alerted several banks to freeze any associated accounts linked to the suspect’s mobile numbers.
Broader Implications and Trends: This incident exemplifies the rising threat of “Search Result Manipulation” where scammers pay for ads or use SEO tricks to appear as legitimate helpdesks. It serves as a stark warning to the public to use only official bank or government apps for FASTag recharges and services. The two-day delay in the theft shows a strategic shift where criminals “sit” on stolen data to lower the victim’s guard before executing the final transfer.