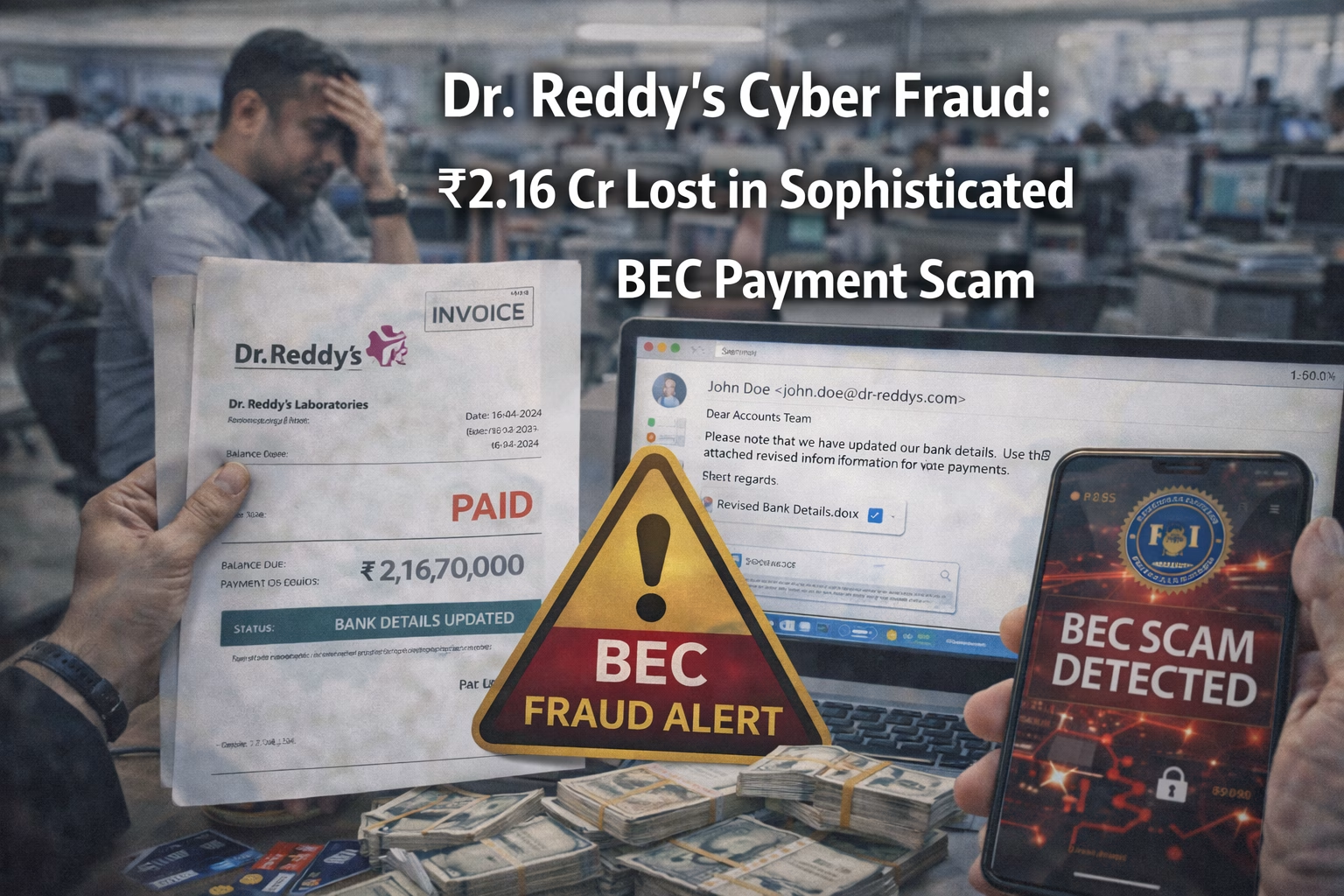
Background and Timeline: In early February 2026, the pharmaceutical giant Dr. Reddy’s Laboratories reported a significant financial loss due to a Business Email Compromise (BEC) attack. The breach was only noticed after the legitimate recipient reported non-receipt of the funds, triggering an internal audit. This incident follows a series of high-profile corporate targeting campaigns identified in late 2025.
Modus Operandi: Fraudsters successfully infiltrated an ongoing email conversation between Dr. Reddy’s and Group Pharmaceuticals. They monitored the thread for several weeks to understand the payment schedule and writing styles. Finally, they impersonated Group Pharmaceuticals officials and provided “updated” banking details for a pending payment, which was authorized by Dr. Reddy’s finance team.
Victims and Financial Impact: The company suffered a direct financial loss of ₹2.16 crore after transferring funds to the fraudulent bank account. Beyond the direct money lost, the breach raised serious concerns about the integrity of the firm’s internal communication infrastructure. The loss underscores the vulnerability of even large, tech-savvy enterprises to sophisticated social engineering.
Investigation and Agencies Involved: Specialized cyber units are investigating the “man-in-the-middle” technique used to monitor the corporate correspondence. Investigators are examining server logs to determine how the initial email access was gained, likely through a phishing lure. They are also tracking the movement of the ₹2.16 crore through a complex network of accounts.
Arrests and Suspects: No arrests have been made yet, as the attackers utilized encrypted channels and overseas jurisdictions to obscure their identity. The investigation is currently focusing on the IP addresses used to log into the compromised accounts. The syndicate responsible is suspected to have carried out similar attacks against other large Indian firms.
Broader Implications and Trends: BEC attacks on major corporations are becoming more sophisticated, involving long-term surveillance before the final strike. This incident highlights the need for robust multi-channel verification for any changes to banking details in corporate transfers. It reinforces that traditional perimeter security is insufficient against identity-led social engineering.