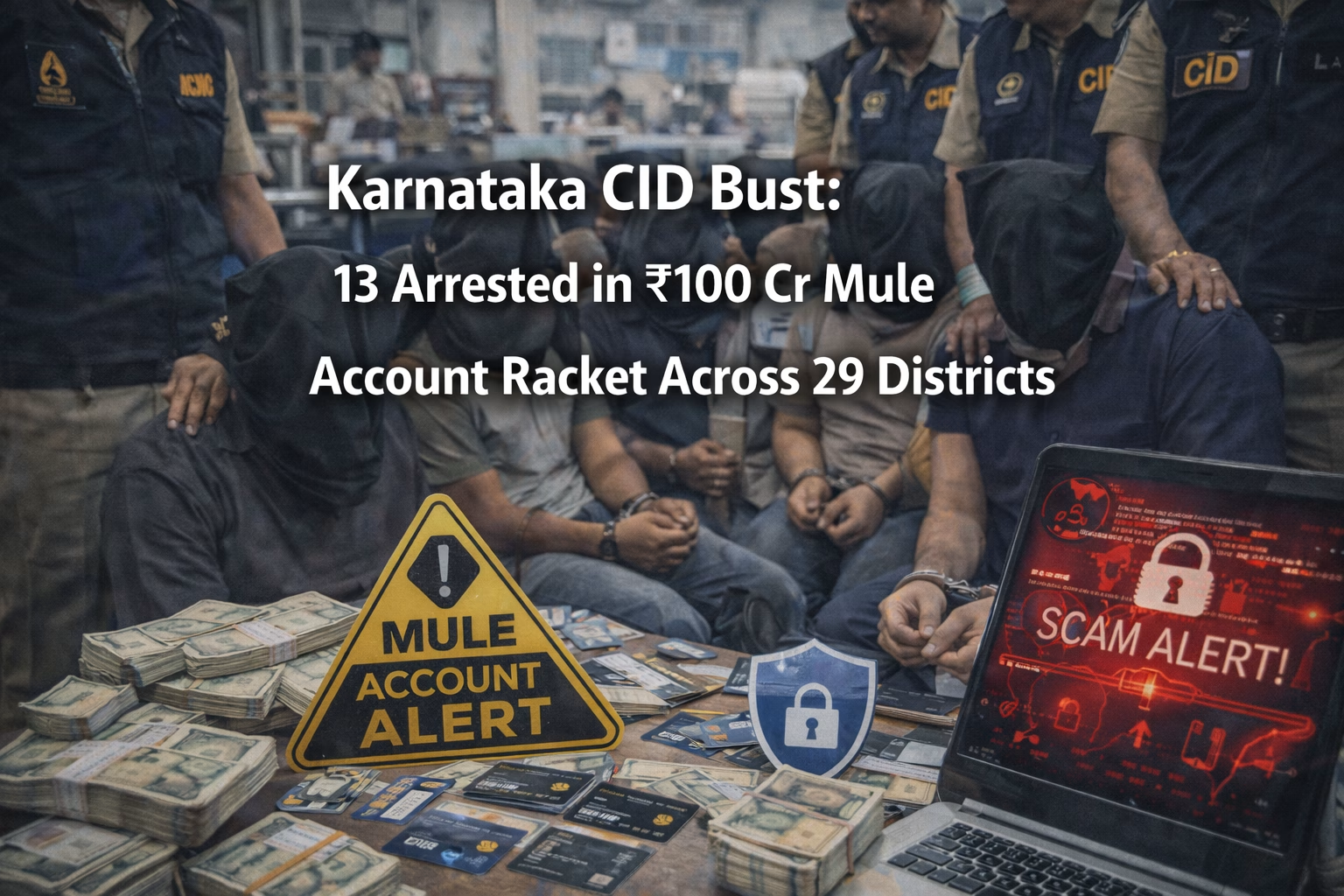
Background and Timeline: Between February 5 and 7, 2026, the Karnataka CID’s Cyber Command Cell executed a massive enforcement operation involving coordinated raids at over 100 locations across 29 districts. The crackdown was initiated as an intensified follow-up to numerous “digital arrest” cases and illegal betting reports that pointed toward a massive internal laundering network. This operation represents one of the most significant state-level actions against the “mule” ecosystem since the establishment of the dedicated command hub.
Modus Operandi: The racket was managed by specialized “mule herders” who recruited economically vulnerable individuals from working-class backgrounds to “rent” out their personal bank credentials. These individuals were paid monthly commissions ranging from ₹10,000 to ₹20,000 to hand over their bank documents, ATM cards, and cheque books to the syndicate. The herders then shared these accounts with international networks involved in illegal betting, investment scams, and digital arrest frauds to distance masterminds from the money trail.
Victims and Financial Impact: Investigators discovered that the network facilitated transactions worth at least ₹100 crore over the past two fiscal years, utilizing a pool of over 42,000 compromised bank accounts. Two primary accused suspects—one from Shivamogga and another from Bengaluru—were found to have personally managed 19 accounts that handled ₹55 crore in illicit flows. Most of the account holders were reportedly unaware that their personal banking identities were being misused for high-value cyberfraud.
Investigation and Agencies Involved: DGP Pronab Mohanty (CID-cyber command) led the task force, utilizing financial trail mapping and digital footprint analysis to link local accounts to kingpins based in Delhi and Dubai. The investigation successfully linked the arrested suspects to 96 distinct cybercrime cases reported across the country, highlighting the interstate reach of the module. So far, nearly 20 FIRs have been registered in connection with this specific herder network as authorities work to dismantle the communication channels.
Arrests and Suspects: Thirteen key masterminds and “herders” were arrested during the two-day state-wide operation, including individuals who served as the primary aggregation hubs for the network. These suspects are currently being interrogated to identify the high-level handlers in Dubai and the specific encrypted platforms used to coordinate the account transfers. Police noted that the kingpins are largely operating from international safe havens to avoid direct physical apprehension within India.
Broader Implications and Trends: The discovery of over 40,000 mule bank accounts reveals a critical and systemic vulnerability in the banking sector’s KYC and real-time monitoring processes. It demonstrates that the most significant barrier to stopping cybercrime is the ease with which criminals can hide behind domestic legitimate banking infrastructure. The case highlights that the “front-end” of cybercrime is increasingly built on the exploitation of the urban working class and vulnerable rural populations.